Building Institutional OTC Infrastructure on Solana: Contra Clear


How We Built a Private, Compliance-First Settlement Platform
Deep dive into Contra Clear OTC, a project Fairway built at the Solana StableHacks hackathon.
When we talk about institutional adoption of crypto, we tend to imagine a single switch-flip moment where banks log in and capital flows. The reality is, however, messier. Institutions don't just need access to liquidity. They need permission to access it. They need to prove who they are, where they operate, and that their counterparty isn't sanctioned before a single dollar moves. And they need all of this to happen without exposing sensitive data to the entire world.
This is the problem we set out to solve when we entered the Solana StableHacks hackathon. And by the end of the hackathon, we had brought Fairway's compliance and identity infrastructure to Solana.
The Problem: OTC Trading Is Broken
Over-the-counter trading accounts for the vast majority of institutional crypto volume. According to the Bank of International Settlements, “The notional value of outstanding over-the-counter (OTC) derivatives rose to $846 trillion at June 2025, up 16% from June 2024. The gross market value of OTC derivatives rose by $5 trillion (+29%) year-on-year (yoy) to $21.8 trillion.”
The infrastructure supporting OTC is stuck between two bad options:
- Centralized OTC desks require trust in a single intermediary. They're opaque, charge wide spreads, and create counterparty risk. If the desk goes down or worse, goes rogue, so does your capital.
- On-chain DEXs offer transparency and self-custody, but they're fundamentally incompatible with institutional requirements. There's no identity layer. No compliance gating. No way to prove your counterparty has passed KYC without doxxing them on a public ledger. And every transaction is visible to front-runners and competitors.
Institutions need a third path, one that is self-custodial, compliant, and private.
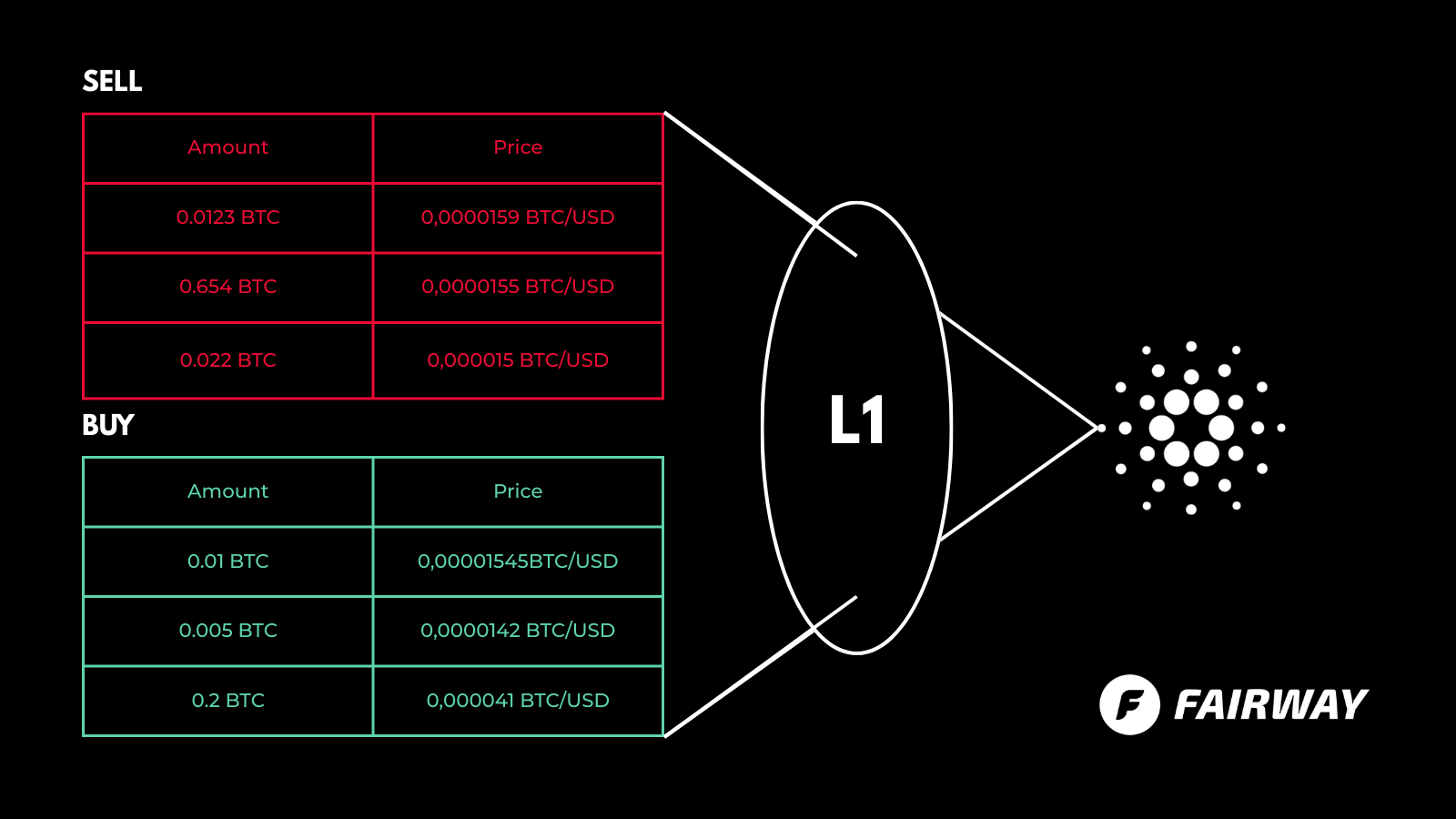
Why Contra
Contra is an enterprise-grade payment channel system built by the Solana Foundation. Contra is neither a sidechain nor a rollup. It's a private transaction channel that settles directly to Solana Mainnet, giving you the security of L1 with the privacy and throughput of a dedicated execution environment. And we found the missing piece there.
Contra processes transactions through a five-stage pipeline: Dedup, SigVerify, Sequencer, Executor, Settler, achieving ~100ms block times with gasless execution. Transactions inside the channel are not broadcast to Solana's public mempool. They're batched, settled atomically, and only the final state transitions hit Mainnet. For institutions, this means your trading patterns, counterparties, and volumes are not visible to competing desks or adversarial observers.
Contra also leverages Solana's SPL Token-2022 Confidential Transfer extensions. These can be extended to use zero-knowledge proofs and homomorphic encryption to encrypt transaction amounts on-chain. Even when settlement data hits Mainnet, the amounts can be masked. Token issuers can then designate auditor keys for regulatory review without exposing data publicly, a critical feature for AML and tax compliance.
Contra leverages Sparse Merkle Trees for secure withdrawal from Contra back to Mainnet. Withdrawals are provably secure without revealing which specific transactions correspond to which withdrawals, preserving privacy even at the settlement boundary.
Our Architecture
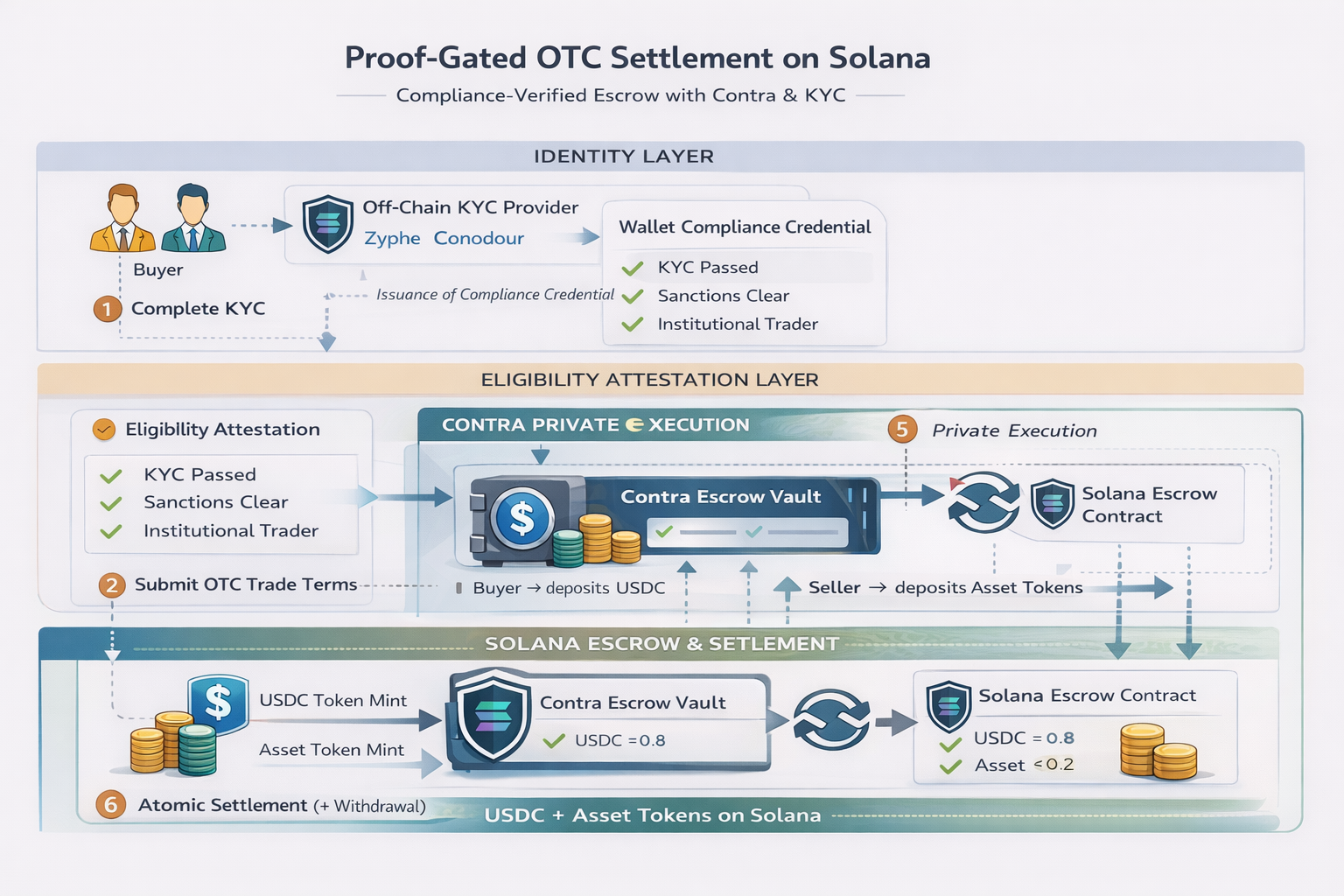
Identity: KYC and KYB Without Surveillance
At Fairway, our founding principle is “compliance without surveillance.” Institutions shouldn't have to choose between regulatory adherence and data privacy. Once the users get verified for KYC/KYB, we write their compliance status to the Solana Attestation Service, an on-chain program that stores structured attestation data without exposing PII. Each attestation is derived as a Program Derived Address (PDA) using the user's wallet as the nonce, one attestation per wallet. Attestations expire after one year and can be revoked if compliance status changes. This is the bridge between off-chain identity and on-chain access control. Smart contracts can read attestation data to gate participation without ever touching personal data.
Five-Tier Compliance Model
Not all institutions are equal. A retail user in Singapore shouldn't have the same trading limits as a Swiss bank. Our tier system reflects this:
| Tier | Label | Max Trade | Accreditation | Jurisdictions |
|---|---|---|---|---|
| 1 | Basic | $10K | Retail | CH, EU, UK, SG, AE, HK |
| 2 | Standard | $100K | Retail | CH, EU, UK, SG, AE, HK |
| 3 | Professional | $1M | Professional | US |
| 4 | Institutional | $50M | Institutional | US |
| 5 | Sovereign | Unlimited | Institutional | CH only (Swiss-regulated bank custody) |
Tier 5 is designed for institutions operating under regulated custody frameworks (e.g., Swiss-regulated banks).
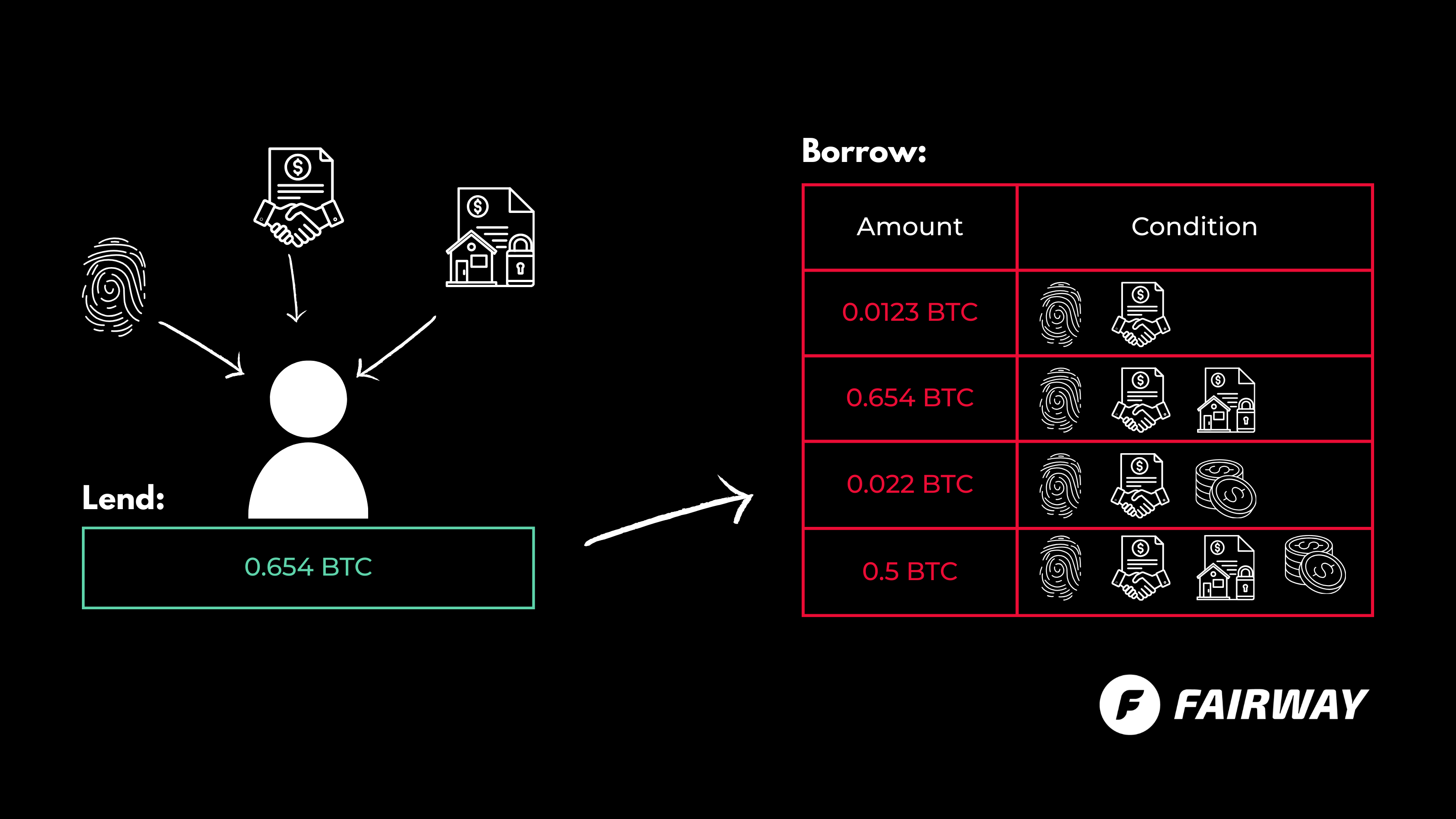
Two Roles, One Market: RFQ Makers and Liquidity Providers
Our OTC platform implements a Request for Quote (RFQ) model with two distinct roles:
RFQ Makers are participants who initiate a trade. They specify:
- Side (buy or sell)
- Asset pair (e.g., EUR/USDT, CHF/USDC)
- Amount and price
- Minimum compliance tier — they can require their counterparty to be at least Tier 3, for example
Before submitting an RFQ, the maker generates a proof demonstrating their compliance tier meets the minimum requirement without revealing their actual tier, jurisdiction, or identity.
Liquidity Providers (RFQ Takers) are participants who fill existing RFQs. They browse the open order book, find a matching RFQ, and generate their own compliance proof. Both parties prove they're qualified without revealing who they are.
Both roles require KYC (for individuals) or KYB (for entities, with the resulting attestation stored on-chain via SAS.
The Trade Lifecycle: From RFQ to Atomic Settlement
1. RFQ Creation
The maker submits their quote with parameters and a freshly generated proof. The proof is submitted on-chain and verified by an oracle. The RFQ is now open. Then, a liquidity provider matches the RFQ by generating their own proof and submitting it on-chain. Once both proofs are verified, an escrow PDA is created on-chain. The maker deposits the base asset; the counterparty deposits the quote asset. Both deposits are locked, and neither party can withdraw unilaterally.
2. Pre-Settlement Checks
Before execution, three automated checks run:
- Price oracle: checks the trade price hasn't deviated more than 2% from the oracle price; in such cases, it notifies the user to be aware of possible manipulated trades.
- Sanctions screening (Chainalysis): Both wallets are checked against sanctioned jurisdictions (KP, IR, SY, CU, VE, MM, BY, RU) and OFAC lists
- Escrow verification: Confirms both deposits are locked and sufficient
3. Atomic Swap
If all checks pass, the swap executes atomically via cross-program invocation (CPI):
- Base asset transfers from maker's escrow to counterparty
- Quote asset transfers from counterparty's escrow to maker
- Both transfers succeed, or both fail — there is no partial execution
4. Nullifier Spending
Each proof contains a nullifier, a unique, deterministic value derived from the proof. Once a trade settles, the nullifiers are marked as spent. This prevents the same compliance proof from being reused across multiple trades, closing a potential double-spend vector on the identity layer.
5. Finality
The escrow is closed, the rent is returned, and the trade is recorded. On Contra, settlement finality is ~100ms. On Mainnet, ~400ms.
Channeling Tokens Into Contra
The flow of tokens between Solana Mainnet and the Contra channel is carefully managed:
Deposits (Mainnet → Contra)
- User approves SPL token transfer
- Tokens are sent to the Escrow Program's ATA on Mainnet (Program:
GokvZqD2yP696rzNBNbQvcZ4VsLW7jNvFXU1kW9m7k83) - The Escrow Program emits a DepositEvent
- An indexer (monitoring via Yellowstone gRPC or RPC polling) detects the event
- The operator mints corresponding tokens on the Contra channel
- User now has a channel balance — usable for private, gasless trades
Withdrawals (Contra → Mainnet)
- User burns tokens on the Contra channel, triggering a WithdrawFundsEvent with a unique nonce
- The indexer detects the event
- The operator generates an SMT exclusion proof (nonce NOT yet in the tree) and then an SMT inclusion proof (nonce now recorded in the new tree)
- The operator submits ReleaseFunds to Mainnet with both proofs
- The Escrow Program verifies the proofs on-chain and releases the original SPL tokens to the user's wallet
The dual-proof mechanism ensures that every withdrawal is accounted for exactly once while keeping the mapping between channel transactions and mainnet settlements obscured.
Stablecoins: The Core Asset Class
This platform was built for the stablecoin economy. We support various stablecoins, including USDC, USDT, USX, AED, CHF, EURC, GBP, JPY, and other mainstream stablecoins.
The focus on stablecoins aligns directly with the StableHacks thesis: Solana is becoming the default settlement layer for institutional stablecoin flows, with over $15B in stablecoin supply and adoption by Visa, Western Union, and others.
KYT: Know Your Transaction
Compliance doesn't end at identity verification. We built a Know Your Transaction (KYT) monitoring layer that gives administrators real-time oversight.
Admin Dashboard
The compliance dashboard tracks:
- Total trades, volume, and settlement times
- Number of verified users
- Individual trade records with per-trade compliance status
Regulatory Frameworks
We track compliance across three major frameworks:
- Travel Rule (FATF Rec. 16): All OTC trades above $1,000 include originator/beneficiary data. proofs enable Travel Rule compliance without PII exposure.
- MiCA (EU Markets in Crypto-Assets): Full transaction logging, reserve attestations, consumer protections via escrow.
- FINMA (Swiss Financial Market Authority): Quarterly reporting ready, KYC/KYB for all counterparties.
Suspension and Banning
When the admin detects unusual activity: anomalous trade patterns, sanctions hits, or compliance failures, they can:
- Suspend a user's DID, temporarily blocking all RFQ creation and matching
- Ban a user, permanently revoking their identity attestation and cancelling all open RFQs
- Review a full audit log of all compliance events, verification results, and trade records
AMINA Bank: Where TradFi Meets On-Chain

One of the most exciting aspects of StableHacks was that AMINA Bank, a FINMA-regulated Swiss crypto bank, was a co-host and challenge partner.
Fairway already operates in the regulated compliance space. We are building identity infrastructure on Cardano and Midnight chains. Participation in StableHacks highlighted a potential pathway for integration with regulated custodians such as AMINA Bank
The Security Model
Let's be precise about what's protecting funds and identity at each layer:
Identity Layer
- proofs prove compliance without revealing PII
- Nullifiers prevent proof reuse across trades
- SAS attestations are on-chain but contain no personal data — only accreditation level, jurisdiction, and tier
Trading Layer
- Escrow locks funds before execution — neither party can withdraw without mutual settlement
- Atomic swaps via CPI ensure all-or-nothing execution. Chainalysis sanctions screening blocks prohibited counterparties
Settlement Layer
- Contra's five-stage pipeline provides deterministic execution ordering
- SMT exclusion/inclusion proofs guarantee withdrawal integrity.
Infrastructure Layer
- Webhook signature verification for KYC callbacks
- DID revocation capability for compromised or non-compliant identities
- Full audit logging of all compliance events
What's Next
This hackathon was a starting point, not a finish line. Our roadmap includes:
- Mainnet deployment — moving from Devnet to Solana Mainnet with audited smart contracts
- Multi-provider KYC/KYB — adding Sygnum, Sumsub, and Onfido
- Chainalysis production integration — moving from mock sanctions checks to live API calls
Final Thoughts
The gap between crypto's promise and institutional reality isn't technical; it's architectural. The primitives exist: proofs, on-chain attestations, confidential transfers, and atomic swaps. What's been missing is a system that composes them into something an institution would actually use.
That's what we built. Not a DEX. Not a centralized desk. A compliance-first, privacy-preserving, self-custodial OTC settlement layer.
Solana isn't just fast. With Contra, Token-2022, and the Solana Attestation Service, it's becoming the kind of institutional-grade infrastructure traditional finance has been waiting for.
If you're building institutional infrastructure on Solana or if you're at AMINA Bank and reading this, reach out at Contact Person or see it live at contraclear.fairway.global

Kaleab Abayneh
Developer specializing in secure smart contract auditing and formal verification. Passionate about writing robust, gas-efficient code that is resilient to exploits, ensuring the reliability of decentralized applications.